Data Governance
An important aspect of Data Management (DM) is Data Governance (DG). A DG framework stipulates how data must be acquired, transmitted, stored, accessed, shared, and destroyed. Anyone who handles data must adhere to these guidelines. It is a myth that only large enterprises that can afford to make a substantial monetary investment can implement and adhere to a good DG framework. As a matter of fact, what it really requires is a commitment to making your data management processes trustworthy and ethical and developing a mindset of vigilance.
Assessment
Any Data Governance implementation must begin with assessment. The goal of such assessment is two-fold. Assessing which aspects Data Governance are relevant to the organisation, how relevant are they, what is the goal in terms of maturity of each aspect and how far along are we currently, or in other words, what is the current maturity level.
Pillars of Data Governance
The four pillars or the most important aspects of any Data Governance framework are Privacy, Quality, Regulatory-Compliance and Security. As such, this framework might differ from other frameworks, say the one stipulated by DAMA, but it covers all the aspects that you need to cover to ensure a robust Data Governance culture. That is to say, by covering these aspects, an organisation can achieve readiness and maturity that would be enough to largely minimise the gap toward achieving a standard certification (like ISO-27001 or NIST).

Relevance and Maturity
A number of factors go into deciding what's relevant or an organisation when it comes to Data Governance and how robust or mature it needs to be. For instance, it could be a straightforward factor like which certification an organisation is aiming for or it could be more like nuanced the demands of industry, customers, partners etc. The 4 pillars may also assume varying levels of relevance based on these factors. Same way, the maturity-level to be achieved is also influenced by these factors.
One more important point to not is that relevance and maturity need to be assessed both at this level and at the next level of "sub-categories" under each pillar. These sub-categories must also be identified based on the demands of the industry, customers, partners etc. For example, some of the sub-categories under security could be "DLP for workstations", "DLP for servers", "Encryption at Rest", "Encryption in Transit" etc., for both Regulatory-Compliance and Privacy, they could be "GDPR Compliance", "CCPA Compliance", "NIST Compliance" etc., and for Quality it be things like "email address cleanliness", "postal address cleanliness" or technical items like "absence of nulls, spaces, special characters" etc.
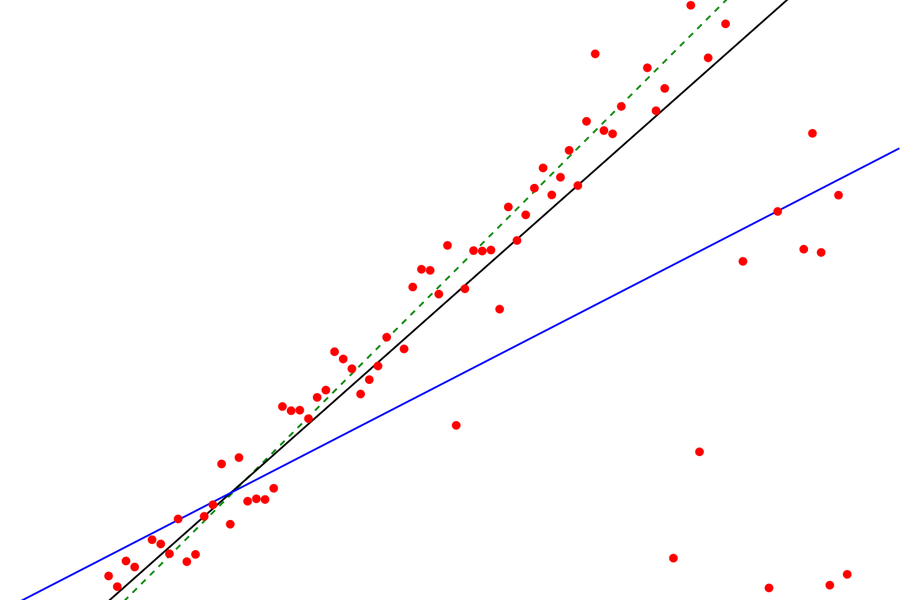
Radar Charts or Spider Plots
All these measurements can be accurately captured, visualised, and understood with the help of Radar Charts. These are also colloquially knows as Spider Plots (because if you colour the shapes formed by the radar lines, they look like spider webs). One interesting aspect is that both relevance and maturity can be depicted in a single image. For example, if we measure the relevance and maturity at the highest pillar-level, the digram might look like this:

Note: I used https://online.visual-paradigm.com/ to draw the beautiful diagrams on this page.
More such content...
Data Pipeline for Customer Success Dashboards
When less is more but bigger is better